This article applies to PRTG Network Monitor 18.1.37 or later
Monitoring Palo Alto Firewalls
PRTG provides some sensor types that work with PaloAlto Firewalls by default, for example, the SNMP Traffic sensor. This template will deploy both some of these standard sensors and custom/specific sensors created specifically for Palo Alto Firewalls such as PA-200, PA-220, PA-3020, PA-5050 and VM-100/200 models.
Adding Custom Sensors Using Auto-Discovery and Template
You can use the device template that we provide below to automatically create the following predefined and custom sensors with the PRTG auto-discovery.
The metrics that are available can vary. The included sensors can monitor the following if the data is available:
- Ping
- Ping time
- Minimum
- Maximum
- Packet Loss
- System Uptime
- Node HA Mode
- Peer HA Mode
- Disk Usage
- Free Space (in %)
- Free Bytes
- Total Bytes
- Memory Usage
- Percent Available Memory
- Available Memory
- Total Memory
- Gateway Statistics
- Utilization
- Active Tunnels
- Session Statistics
- Utilization
- Active Sessions (total)
- Active Sessions (TCP)
- Active Sessions (UDP)
- Active Sessions (ICMP)
- SSL Proxy Statistics
- Utilization
- Active Sessions
- Temperature
- Fan Status
- CPU Usage
- One channel for load of each processor
- Total Load
The device template creates the available and compatible sensors based on the data at hand. The sensors implement default alerts whenever possible, but you can still fine-tune most channels by defining additional limits in the sensor channel settings or by modifying the lookups that are included by default.
Requirements
- PRTG Network Monitor 18.1.37 or later
- Because the device template relies on the auto-discovery process, the device you want to monitor needs to be reachable via ping.
- SNMP must be enabled and the device must support the PAN-COMMON-MIB for the Palo-Alto specific sensors.
Known Issues and Limitations
- PRTG shows the alerts as reported by the monitored device via SNMP using lookups. If the status is not reported correctly via SNMP, PRTG cannot detect any issues. For additional alerts, set up limits for additional channels.
- This device template was created based on data collected from other customers, so we cannot guarantee that the sensors described above will work on your systems or that the default thresholds are optimal for your use case. Use these components at your own risk. Please test and validate the sensors in your environment after deploying them.
- The "PhysSensor" sensors are index-based, this means that if the device reboots or is updated the indexes may change. If this happens the sensors may no longer work properly. If you update the device, delete these sensors (PhysSensor) and re-run the auto-discovery afterwards.
Deployment and Usage
- Download the ZIP archive that contains the template files https://gitlab.com/PRTG/Device-Templates/PaloAlto/-/archive/master/PaloAlto-master.zip.
- Extract the archive and copy the content of the folder \PRTG to your PRTG program directory. By default, this is %Program Files (x86)%\PRTG Network Monitor\
- In PRTG, restart the core server: open Setup | System Administration | Administrative Tools | Restart Core Server and click Go!. This ensures that the MIB and lookups are loaded before you run the auto-discovery.
- Create a new device in PRTG with the address (IP or FQDN) of the device that you want to monitor and configure the SNMP credentials accordingly.
- Right-click your new device, select Run Auto Discovery with Template, browse for palo and select the Custom Palo-Alto Firewall v0.3 template from the list.
Note: Using the auto-discovery with a dedicated device template is convenient here because it automates the creation of the custom sensors in an organized fashion.
- The sensors are deployed after a couple of seconds.
- You can modify the channel limits or lookups later as necessary.
Result
The created sensors will look like this:
Sensor's Overview
Device Overview
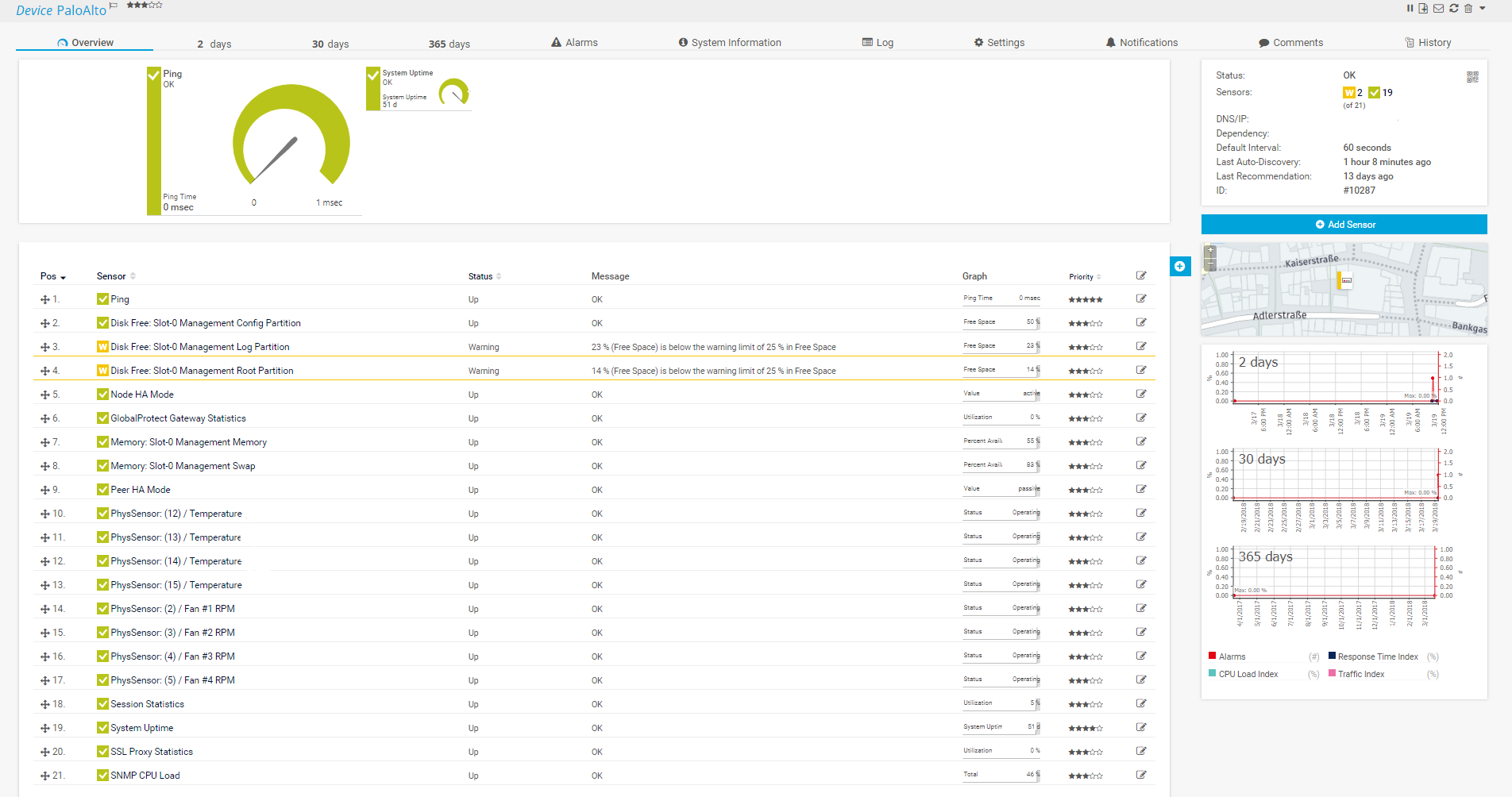 Right-click and select Open Image in New Tab for full-screen view
Right-click and select Open Image in New Tab for full-screen view
Session Statistics Sensor Overview
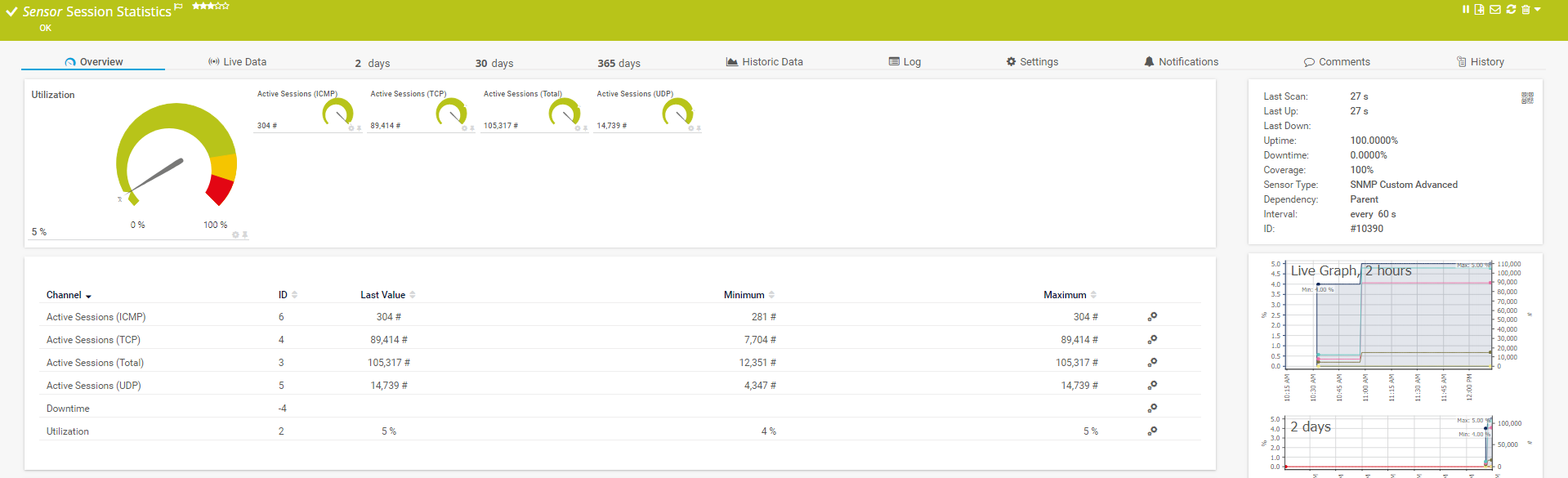 Right-click and select Open Image in New Tab for full-screen view
Right-click and select Open Image in New Tab for full-screen view
No sensors deployed? :(
Please read ahead for troubleshooting.
Troubleshooting
Have any issues? Please don't hesitate to contact us by replying to this post or via a support ticket. Please make sure to mention this article. Read ahead for troubleshooting steps that you can take in advance.
Auto-Discovery Log
Your auto-discovery log tells you a lot about what went wrong during the sensor's deployment. You can troubleshoot the auto-discovery by inspecting the auto-discovery log. If you get entries like the one below (NOT FOUND), it means that the required protocol or Object Identifier (OID) is not available and the sensors can't be deployed.
[...]
3/7/2018 10:54:17 AM: Template Loaded; Device ID: 10287; Name: Custom Palo-Alto Firewall v0.3
3/7/2018 10:54:18 AM: Template Check; Device ID: 10287; Check ID: ping; FOUND
3/7/2018 10:54:18 AM: Template Assigned; Device ID: 10287; Name: Custom Palo-Alto Firewall v0.3
3/7/2018 10:54:18 AM: Sensor Created; Device ID: 10287; Create ID: pingsensor; Sensor ID: 10341; Name: Ping
3/7/2018 10:54:19 AM: Template Check; Device ID: 10287; Check ID: snmp; FOUND
3/7/2018 10:54:20 AM: Template Check; Device ID: 10287; Check ID: snmpdiskfree; FOUND
3/7/2018 10:54:24 AM: Template Check; Device ID: 10287; Check ID: snmp_entPhySensorTable; NOT FOUND
[...]
In the example above, some sensors were skipped because the device did not respond to the snmp_entPhySensorTable check. This means that this data is probably not available on your device. You can track this data by looking for the name after snmp_. In this case, a search for entPhySensorTable will tell you what OID from what MIB is missing.
You can also use this log to identify if the discovery was interrupted because the device did not respond to ping or to a basic SNMP check.
SNMP Data
If the discovery log is not sufficient, you can review the SNMP data directly from your device. To do so, save the text below (in the white box) as .txt and use it with the Scan Script option in our SNMP Tester. This will allow you to review which SNMP queries succeed and which do not deliver any data. Please have this information at hand when contacting our support team.
--------
Walk Default
--------
hrSystemUptime
walk=1.3.6.1.2.1.25.1.1
--------
MIB-2 System
walk=1.3.6.1.2.1.1
--------
Sensor Specific Queries
----
panGPGatewayUtilization
walk=1.3.6.1.4.1.25461.2.1.2.5.1
---
panSession
walk=1.3.6.1.4.1.25461.2.1.2.3
---
entPhySensorTable
walk=1.3.6.1.2.1.99.1.1
---
panSys
walk=1.3.6.1.4.1.25461.2.1.2.1
---
Add comment